The fatal collision between a Frontier Airlines aircraft and an unauthorized individual during a takeoff roll at Denver International Airport (DEN) exposes a catastrophic failure in the "Swiss Cheese Model" of aviation safety. Aviation security is predicated on the assumption that the sterile area—the space beyond TSA checkpoints and perimeter fencing—is a controlled environment where every moving variable is accounted for by Air Traffic Control (ATC) or Ground Operations. When a non-compliant human element enters the active runway environment (the runway safety area or RSA), the margin for error collapses to zero. This event is not merely a localized tragedy but a data point revealing a critical bottleneck in the real-time detection of perimeter breaches during high-velocity flight phases.
The Kinematics of Takeoff Incursion
The physics of a commercial jet during its takeoff roll render pilot intervention practically impossible once the aircraft reaches a specific velocity threshold. For an Airbus A321 or similar narrow-body aircraft, the V1 speed—the maximum speed at which a takeoff can be safely aborted—is often between 140 and 160 knots.
The mechanics of this specific fatality involve three distinct physical variables:
- Visual Blind Spots: During the rotation phase, the pitch of the aircraft increases, significantly obscuring the pilot’s view of the ground immediately ahead of the nose gear.
- Thermal and Acoustic Displacement: At takeoff thrust, the engines generate massive decibel levels and heat signatures that can disorient an individual on the ground, making it unlikely they can accurately judge the closing speed of an approaching aircraft.
- Kinetic Energy Transfer: The force of an impact at 150 mph is absolute. Given the mass of the aircraft (roughly 170,000 to 200,000 lbs), the deceleration required to avoid an object detected within 500 feet is physically unattainable under current braking and reverse-thrust configurations.
Failure Points in Perimeter Integrity
A secure airport perimeter relies on a layered defense-in-depth strategy. To understand how an individual reached an active runway at one of the world's busiest hubs, we must analyze the three structural layers of airside containment.
The Physical Barrier Layer
The primary defense is the 10-foot chain-link fence, often topped with three-strand barbed wire or concertina wire. While effective against casual trespass, these barriers are "passive" and "dumb." They offer no active feedback if breached via cutting or climbing unless integrated with a Perimeter Intrusion Detection System (PIDS). At an airport with the geographic footprint of Denver—covering 53 square miles—maintaining 100% real-time sensor coverage across the entire fence line presents a massive infrastructure cost and a high rate of false positives caused by local wildlife or weather.
The Surveillance and Detection Layer
Modern airports utilize a mix of Ground Movement Radar (GMR) and Airport Surface Detection Equipment (ASDE-X). ASDE-X is designed to track aircraft and transponder-equipped vehicles to prevent runway incursions between authorized users. Its limitation lies in its inability to consistently differentiate a single human body from "clutter" or ground noise, especially if that individual is moving near the runway edge where radar returns are often filtered to prevent screen saturation for controllers.
The Human Response Lag
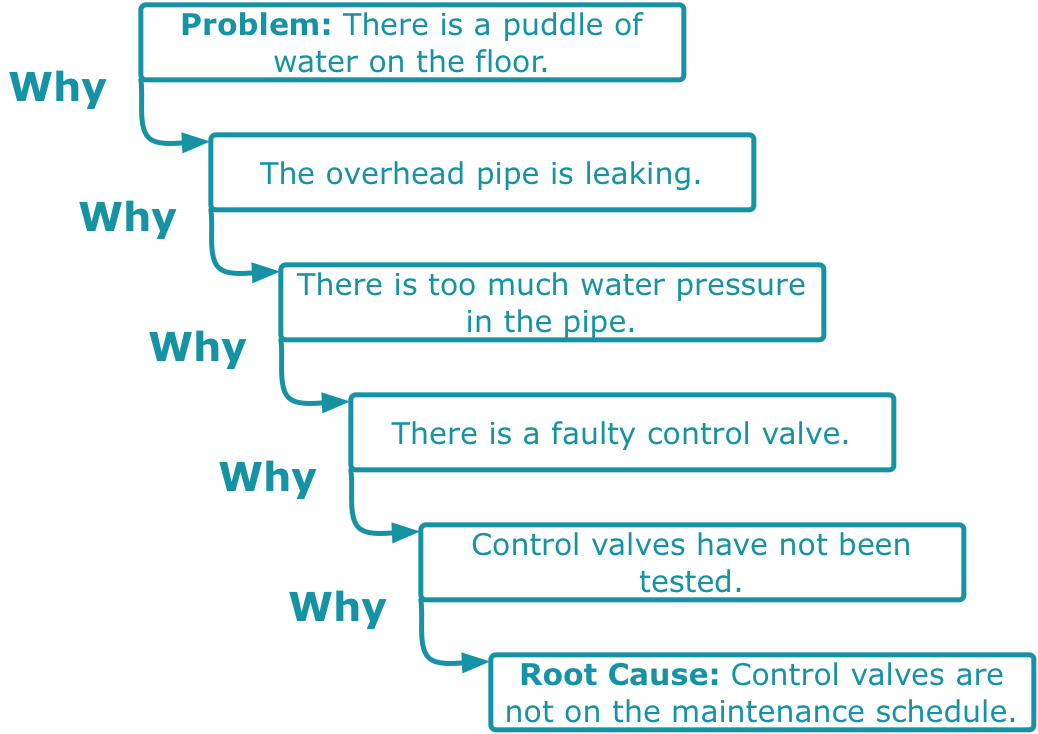
Even if a camera captures a breach, the "Detection-to-Action" cycle often exceeds the time required for an individual to reach a runway.
- T0: Perimeter breach occurs.
- T1: Breach is identified by security or automated software.
- T2: Communication is relayed to the FAA control tower.
- T3: Controllers issue an emergency hold or go-around order.
In high-tempo environments like Denver, the duration between T0 and T2 can span several minutes, while an individual can traverse the distance from a perimeter fence to a runway in under 120 seconds.
The Economic and Operational Cost Function
While the loss of life is the primary concern, the secondary impacts of a runway fatality create a ripple effect across the National Airspace System (NAS). We can categorize these impacts into three specific buckets:
Operational Paralysis
An active runway involved in a fatality becomes a crime scene. Federal Bureau of Investigation (FBI) and local law enforcement protocols require the preservation of evidence, which often leads to the closure of that specific runway for 4-8 hours. At a hub like DEN, the loss of one runway reduces throughput by approximately 25-33%, causing multi-state delays as inbound flights are diverted or held at their origin.
Fleet and Crew Maintenance
The aircraft involved must be removed from service for a "Strike Inspection." This includes checking the landing gear assemblies, engine inlets, and the fuselage for structural damage or biological ingestion. The cost of taking a $100 million asset offline, combined with the mandatory psychological grounding of the flight crew, creates a direct hit to the airline's "Available Seat Miles" (ASM) profitability.
Insurance and Liability Escalation
These incidents trigger rigorous audits of an airport’s Part 139 certification. If investigators find that a known gap in the fence was left unrepaired or that a PIDS system was deactivated due to maintenance, the liability shifts from "unforeseeable accident" to "negligent security," exponentially increasing the potential settlement costs and future insurance premiums.
Logic Gaps in Current Security Paradigms
The prevailing logic in airport security has historically focused on the "Inside-Out" threat—passengers carrying contraband or employees with badged access. The Frontier incident highlights the "Outside-In" threat, which is often under-resourced.
The industry currently faces a "False Positive Paradox." If sensors are too sensitive, they trigger hundreds of alarms for tumbleweeds or coyotes, leading to "alarm fatigue" among security personnel. If they are not sensitive enough, they miss a human breach. The missing link is the integration of AI-driven computer vision (CV) that can classify objects in real-time. Without automated classification, the perimeter remains a vulnerability that relies on the "lucky" timing of a human guard looking at the right monitor at the exact moment of a breach.
Categorization of the Breach Mechanism
To prevent recurrence, the investigation must determine which of the four "Breach Archetypes" occurred:
- The Maintenance Gap: Failure of the physical structure due to erosion, weather, or delayed repair.
- The Vehicle Portal Exploit: Tailgating an authorized vehicle through a security gate or entering during the gate’s cycle time.
- The Over-the-Top Incursion: Scaling the fence using improvised tools or natural high points.
- The Internal Transition: An individual who was legally in a non-sterile area (like a parking lot or terminal) and found an unsecured door leading to the ramp.
Each of these requires a fundamentally different mitigation strategy. A maintenance gap is a budgetary and scheduling failure; a vehicle portal exploit is an operational training failure.
Strategic Realignment of Airside Safety
The goal of airport operators must shift from "Perimeter Hardening" to "Active Area Domination." Hardening is a static strategy that eventually fails; domination is a dynamic strategy that uses technology to ensure that no unauthorized movement occurs within 1,000 yards of an active runway without triggering an automated stop.
The most effective path forward involves the deployment of Low-Earth Orbit (LEO) satellite monitoring or high-altitude drone patrols integrated with the airport’s lighting system. Imagine a scenario where a perimeter breach automatically triggers high-intensity LED strobes along the nearest runway, signaling pilots to "Abort/Do Not Enter" before the tower even speaks. This bypasses the Human Response Lag entirely.
Airport authorities must now treat the perimeter not as a fence, but as a digital sensor array. The transition from "watching" to "sensing" is the only way to close the gap between an unauthorized entry and a high-speed takeoff roll. Failure to integrate these systems means that the safety of millions of passengers remains dependent on a 20th-century solution—a chain-link fence—to solve a 21st-century security crisis.
The immediate tactical play for airport management is the implementation of "Incursion Buffer Zones." These are secondary, internal infrared barriers located 100 feet from active taxiways. Unlike the external perimeter, which is subject to public interference, an internal buffer zone has a near-zero false-alarm rate. Any trigger in this zone is, by definition, an emergency, allowing for an immediate "Flash Freeze" of all ground movements. This moves the trigger point closer to the aircraft, but increases the reliability of the alarm, ensuring that when the system screams, it is for a legitimate threat.